We have already learned docker networking in one of our previous articles. But the scenario is not the same as here because here we are deploying docker containers on a swarm cluster.In this article we will learn how docker networking works on swarm cluster.
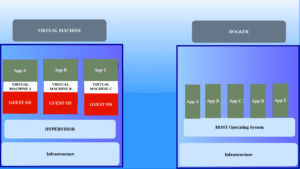
Docker provides three main types of networks that can be used to facilitate communication between containers:
- Bridge Network: The bridge network is the default network that Docker creates when you install it. Containers connected to the bridge network can communicate with each other using IP addresses. By default, containers in the bridge network can communicate with each other, they can be exposed to the public by pushing a port. Here we have a docker host port and container port mapping
- Host Network: In the host network mode, containers share the network namespace with the host machine. This means containers bypass Docker’s network isolation and directly use the host’s network stack. For example, if a web server is running inside a docker container using the host network uses port 80 of the host also.
This might cause the container ports to conflict with each other. - Overlay Network: Overlay networks are used for multi-host communication in Docker swarm mode. They enable containers running on different hosts (nodes) to communicate with each other seamlessly as if they were on the same network.
Learn more about the bridge and host network from our previous article
Docker Networking
Overlay networking
We have already learned about swarm clusters. In the docker swarm cluster, we might have multiple nodes so how does a web container from one host communicates with the DB container on another host is where the overlay network comes into the picture.
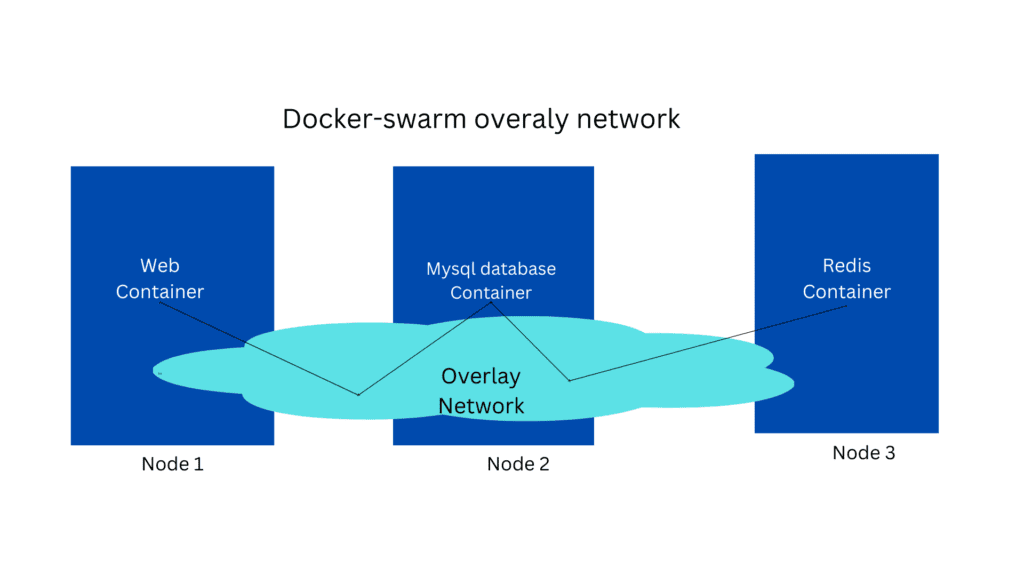
As you can see in the above image the web and database are in different nodes . If the web and database are on the same machine they can communicate with each other using the docker bridge network but here the containers are communicating using the docker overlay network.
We can create a docker overlay internal network that spans across all the nodes in the cluster using this command
docker network create –driver overlay –subnet <internal_ip/cidr> myoverlay-network
And you can attach that network to our service using the below command
docker service create –replica=2 –network myoverlay-network nginx
The most commonly used private IP address ranges are:
- 10.0.0.0 to 10.255.255.255 (10.0.0.0/8)
- 172.16.0.0 to 172.31.255.255 (172.16.0.0/12)
- 192.168.0.0 to 192.168.255.255 (192.168.0.0/16)
In this way, containers can communicate with each other even if they are on different nodes.
Now let’s talk about another type of networking called ingress networking.
Ingress networking
We have already learned about port publishing and port mapping. Suppose we have a webserver running on port 80 so if an external user needs to access the container we should map the container port to the docker host port but image if the same container is deployed on the swarm cluster with only 1 node.
And suddenly if we increase the replica count to 2 it will still continue to work but we have already learned that 2 containers cannot share the same docker host port so how is that possible?
docker service create –replica=2 -p 80:80 nginx
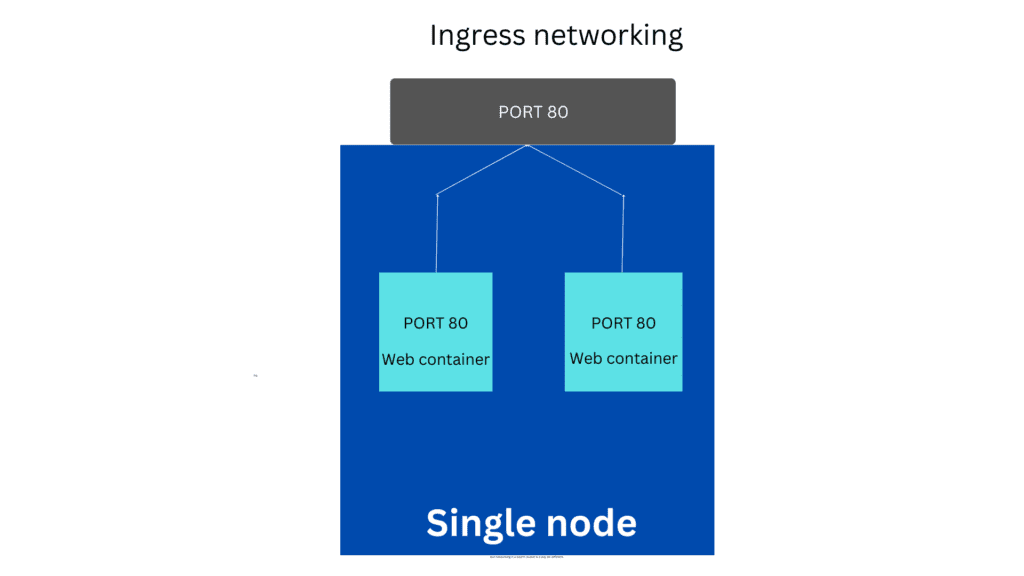
As you can see in the above image both the containers are trying to map to port 80 on the docker host as both the container are on the same node with 2 replicas.
When you create a docker swarm cluster it automatically creates a ingress network behind the scenes so in this case this ingress network has a build load-balancer that redirects the traffic to both the container so it redirects the traffic from host port 80 to both containers running on port 80.
Since this ingress network is created automatically there is no additional configuration is needed from our end. You need to just create the service and mention the replica count the ingress network will work out of the box.
Summary:
In this article, we have covered a high-level overview of docker-swarm networking.